PHDays 11 wrap-up: interest in information security explodes, Rutube attack investigated, pipeline shutdown demo
5/20/2022
Information security is directly linked to the security of the general public and the entire state. This was underscored repeatedly at the international practical security forum Positive Hack Days 11. A live demonstration took place as part of the world’s biggest open cyberbattle, The Standoff. The events were the most watched in their history: over 127,000 online viewers and participants and 8,700 visitors on-site in Moscow.
The PHDays 11 program included around 100 talks, discussion sections, and round tables, contests with cash prizes (for example, hacking an ATM, a POS terminal, or a cash register), the creative festivals Positive Wave and HackerToon, the final of the first All-Russian open-source project competition for schoolchildren and students, a cyberart theft competition, and much more besides.

Here are some of the incidents instigated by attackers during the four days of The Standoff: oil production stoppage (in the infrastructure of the oil and gas company Tube, which is engaged in oil and gas production, refining, storage, and sale), oil-product pipeline shutdown, disruption of wastewater treatment facilities. The triggering of such threats in real life could have the gravest consequences. The attacks on the Ferris wheel, the jet bridge, and many other facilities of the virtual State F were brought to their logical conclusion.
The hackers actuated a total of 63 unacceptable events, 30 of which were unique. For comparison: in the November cyberbattle, only six unique unacceptable events were triggered. Almost all companies suffered, with the exception of the banking system. Of the 17 red teams, 14 managed to disrupt the railway ticketing system. In addition, malware was introduced into the development process.
The winners of the cyberexercise on the attacking side were the Codeby team (27,715 points), with True0xA3 in second place (23,381 points), and Invuls in third (12,352 points). During the four-day event, the attackers submitted 295 vulnerability reports. About 40 percent of these reports were sent by Codeby, DeteAct, and Bulba Hackers. Most vulnerabilities were detected at the Heavy Logistics shipping company.
Over the four days, the defenders submitted 287 incident reports and 10 investigation reports. The ZoneZone team turned in the most reports. The minimum investigation time was one hour and 13 minutes; the average was nine hours and 15 minutes.
"Participation in The Standoff is always beneficial for us," said Nikolay Nashivochnikov, Deputy CEO and Technical Director, Gazinformservice, on behalf of the defenders. "Members of GiSCyberTeam uncover and investigate incidents in conditions that are even more severe than real ones, with more restricted protection functionality. Today, large-scale cyberattacks on critical information infrastructure are almost non-stop. In the current context, these cyberexercises are a great opportunity to apply one’s skills and develop attack prevention strategies. Enterprises and business structures in Russia are facing ever more cyberthreats, so, as information security professionals, we treat this event like work. Monitoring and investigating information security events is fascinating and exciting, but it’s still a job."
How Rutube was attacked
Towards the evening of day two of PHDays 11, guests of the forum’s on-air studio shared details of the May attack on the video hosting service Rutube. Alexander Moiseev, Deputy CEO of Gazprom-Media Holding, stated that the service infrastructure had suffered considerable damage, but user data had been left untouched, which clearly indicates that the cybercriminals’ aim was to completely destroy the video platform. Alexey Novikov, Director of the Positive Technologies Expert Security Center (PT ESC), whose team is investigating the incident, noted that the attackers used publicly available tools, including Cobalt Strike, which is used by many pentesters, as well as traditional system administrator tools. Alexander Moiseev added that Gazprom-Media Holding plans to hold a session at the upcoming St. Petersburg International Economic Forum, where he will talk in detail about the incident in terms of its impact on users.
"PT ESC analyzes the technical traces left by cybercriminals in the infrastructure, and thus reconstructs the entire chain of events," said Alexey Novikov. "The answer to the question of how this attack was carried out is crucial. It will ensure that such attacks never occur again."
How investigators look for information
Any action on a computer leaves a digital trace: opening, reading, modifying, deleting files; accessing a network; opening ports, and so on. This was brought up by Daniil Borislavsky, Head of Implementation at Atom Security, who presented the report "Investigating infosec incidents caused by employees: where to look, what to grab, how to catch" in the business track.
"Such information stays on the computer, but there’s an awful lot of it," he explained. "You need search tools. The first of these is attribute search, which is fast, but only searches the outer properties of the files. The second is content search, that is, looking inside files. But this method is time-consuming and not every file can be opened."
"Today, when searching for information in images on a PC, incident investigators use OCR technology to translate data into text form. What’s more, it is not rational to analyze everything and anything, so dictionaries and regular expressions are needed. Another approach is to use neural networks. With their help, we were able, for example, to sort through and find scans of passports online," noted Daniil Borislavsky.
Banks set up crisis response groups
On-air studio guests also discussed the importance of cybersecurity for finance industry executives.
Roman Chaplygin, Director of Business Consulting at Positive Technologies, spoke about the emergence of full-fledged cybersecurity crisis response teams at companies, which can include not only leaders, but ordinary employees with various skillsets.
"If previously cybersecurity was at the bottom of the list of priorities, now top management is tackling the problem head-on: crisis committees are being set up, and companies are identifying potential targets and attack consequences," he stated.
Independent expert Pavel Klimovich pointed out that bank executives are now focused on real threats. Prior to 2022, the list of such threats numbered up to a hundred. Now many companies are in the process of reassessing the actual risks, those that are really critical.
AI to lend a hand
The potential of artificial intelligence was discussed in the on-air studio by Igor Pestretsov, Advanced Technologies Specialist at Positive Technologies, and Mikhail Trofimov, DataGym lecturer and a Kaggle Grandmaster. The experts spoke about the application of artificial intelligence in various areas of life, including information security, about future growth in the use of neural networks, and about the transformation of many jobs and professions.
"Artificial intelligence will very soon ease the cognitive load on infosec experts, allowing them to focus on really important issues, not on routine," Igor Pestretsov believes.
"We will see the development of general-purpose AI models, each of which can be trained once and its knowledge used in various tasks. There will be many different applications in the most unexpected areas, where such models will show good results right away. Therefore, I expect not so much qualitative as quantitative growth in the use of artificial intelligence," reckons Mikhail Trofimov.
How to build a SOC by effectively combining SOAR and SIEM

The number of infosec incidents has climbed significantly since February, increasing the load on SOCs. The leading presale manager of Security Vision Angelica Svoykina spoke about the use of SOAR systems to close infosec incidents.
"SIEM often produces tens of millions of incidents per day. Compared to Q1 2021, the number of incidents has more than quadrupled. Despite this, the share of smart and sophisticated attacks has fallen: many ordinary users connect to botnets or follow instructions in attackers’ Telegram channels. And if previously attack duration was measured in minutes, since February the average duration has increased to several hours, and many attacks last for several days. All this is creating a huge workload for SOC analysts," she remarked.
In her opinion, this load can be reduced through the interaction of SIEM and SOAR platforms, with the use of ticketing, incident management automation, connectors, and other measures.
Thieves disguised as hacktivists
In recent months, Russia has seen a rise not only in hacktivism, but in financial attacks on Russian companies, which are currently seen by the world hacking community as fair game. This was reported by Oleg Skulkin, Head of Digital Forensics and Incident Response Team, Group-IB.
After 01111111day, information security landscape started to change quickly and locally
In his talk, Kaspersky’s Chief Security Expert Sergey Golovanov presented data from late winter 2022 obtained using Kaspersky’s statistics system, examined cyberincidents, and talked about the tactics and methods used by the perpetrators.
There have been significant changes in information security since February 23, 2022. The field was changing gradually and globally during the COVID-19 pandemic, but this year everything changes very quickly and locally, Sergey noted.
"You can see 01111111day in Kaspersky Security Networks statistics. There wasn’t a single scam phone call made in Russia on February 24. The scam calls eventually came back, but they still haven’t reached the volume we saw in early February. Why is that? For example, on April 15 there was a news story on TV about a den of scammers in Berdyansk, who were tricking Russian people. You can probably guess who was behind it," said Sergey Golovanov. "According to data from our dark web search engine, the number of dark web ads referring to Russian banks decreased sharply that day, then immediately shot back up again, but now they’re gone back down to zero."
On-premise SOC: how to build it without pain
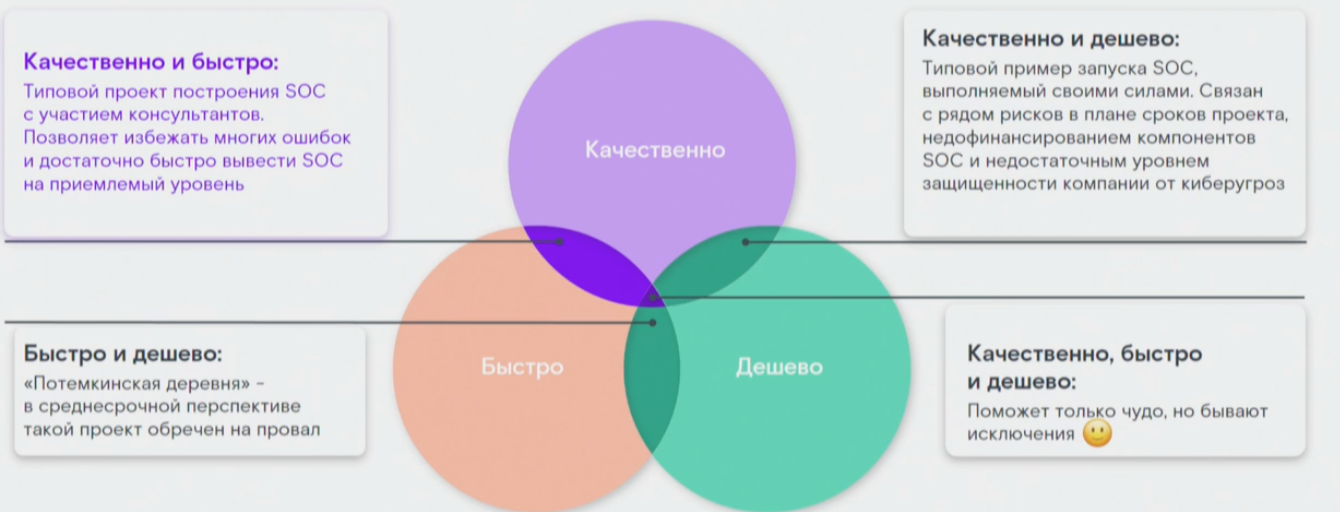
Not all clients are willing to outsource their SOC, so they try to build one locally. Aside from geopolitical necessity, many companies have been categorizing, planning, and deploying information security systems over the last few months and getting ready to start monitoring their own infrastructure and interacting with NCIRCC. The third catalyst is connected to the President’s executive order from May 1 entitled "On additional measures for ensuring information security in the Russian Federation." "When a company builds a SOC, the first thing it usually does is hire a consultant who can avoid repeated mistakes and unnecessary expenses. But if this person leaves, the company can find itself up a creek without a paddle and start running into problems as they develop their SOC. If they try to do it quickly and cheaply, that has its own risks. Everything might look fine on paper—the components are there, there’s content in the SIEM—but the very first penetration test will reveal that the SOC can’t actually see anything," noted Andrey Proshin, Department Head of Solar JSOC, Rostelecom-Solar.
Modern data center: what is it like?
Airat Mustafin, CEO of the IT outsourcing company Liberum Navitas, talked about data centers of tomorrow, pointing out that they have reached a new level of development and will follow banks and websites in becoming ecosystems, interacting with communities and individuals in a number of different ways. "The things we use right now were created a long time ago. That goes for data centers—a lot of them are located in former warehouses, communication centers, and other facilities that weren’t intended for that purpose. Even nowadays, data centers are still built out of sandwich panels. Moreover, most data centers in Russia are in the western part of the country. There aren’t any east of the Urals. Modern data centers need, at minimum, a high level of automation—for example, servers can be moved between racks by robots," said Airat Mustafin.
Building an incident management process under the MSSP model
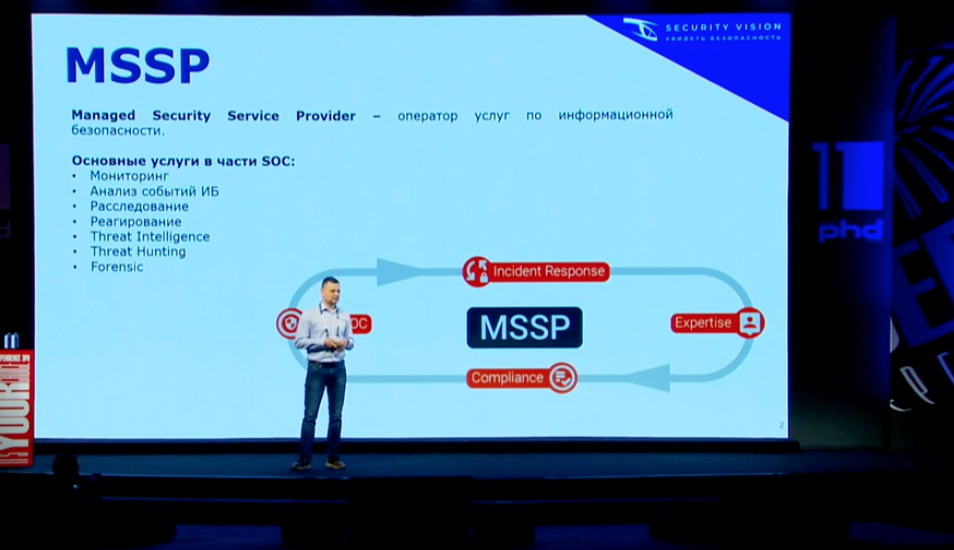
Roman Ovchinnikov, Head of Execution Department at Security Vision, discussed the principles of incident management in the MSSP model, focusing on issues related to building client interaction, methods for providing services, problems inherent in geographically distributed infrastructures, and the finer points of reporting. "There have been two major growth phases in the MSSP market recently. The first one was connected to the pandemic and the large-scale transition to remote work, and the second was connected to what happened in February," said Roman.
Hunting for modern attacks on Active Directory infrastructure
During the technical presentation track, Teymur Kheirkhabarov and Demyan Sokolin from BI.ZONE admitted that they had been planning to talk about all known public attacks on Active Directory infrastructure and accompanying services from 2021 and 2022, but while they were getting ready for the presentation, they realized that an hour just wasn’t enough time to discuss it. So they decided to focus on attacks on Active Directory Certificate Services and discuss the most interesting and effective techniques used by intruders from the perspective of blue teams and SOCs. They also talked about how to detect these techniques via standard Windows logs and which correlation rules can be created in the SIEM system.
Active Directory infrastructure and related services are now an inextricable part of almost every corporate network. As a key infrastructure element, Active Directory is a tempting target for intruders. Maximum privileges obtained within the domain open doors to the infrastructure for attackers—or, if those "doors" aren’t integrated into Active Directory, it still becomes easier to open them.
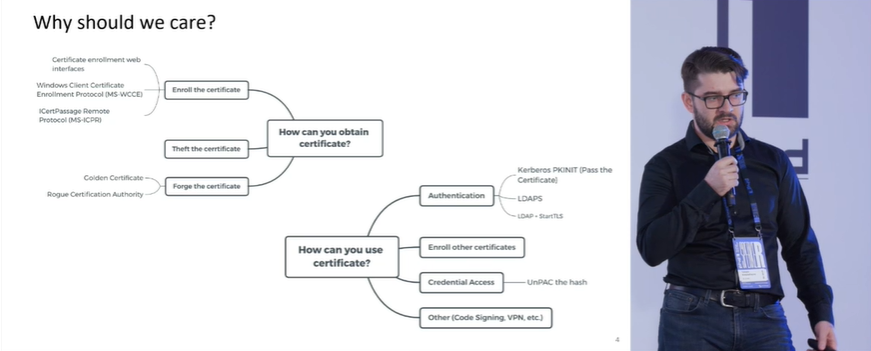
"From the perspective of Microsoft CA services settings, it’s just hell," Teymur acknowledged. "Needless to say, that’s if they’re properly configured and not just ’Next, Next, Done, go to production’. It’s a complex, comprehensive system with lots of parameters that, if improperly configured, can lead to the domain being fully compromised."
More about secure development
Alexey Zhukov (Head of DevSecOps Development, Positive Technologies), Alexey Babenko (Deputy Manager of Engineering, National Payment Card System), and Vladimir Kochetkov (Head of R&D for Code Analyzers, Positive Technologies) talked about what secure development means in information security and why it’s important.
Participants shared their visions for secure development in information security and how to get developers to write bug-free code.
"An application’s security should start with the architecture-planning phase and end with deployment. This means that the product should be secure at every stage of development," said Vladimir Kochetkov.
Alexey Zhukov discussed the importance of dialog with developers and the need to motivate them in various ways to write secure code.
"You need to get people invested in writing bug-free code. Developers can have all sorts of different motivations, from getting a raise to increasing their value on the labor market. Non-financial motivators are important too," said Alexey.
Alexey Babenko noted that developers’ well-known skepticism of security professionals will pass once security becomes part of the development process.
Bug bounty through the eyes of developers, users, and hackers

Round table participants discussed the development of Russian bug bounty platforms (including The Standoff 365 Bug Bounty). Their discussion touched on launch issues, setting rewards for hackers, budgets for searching for and eliminating vulnerabilities, and the market’s future potential. We should mention here that 250 white hat hackers signed up on the platform during the first two days of its operation. Russian private grocery chain Azbuka Vkusa and Positive Technologies were the first companies to put their programs on the platform.
Yaroslav Babin, Director of The Standoff 365, Positive Technologies, talked about rethinking the approach to bug bounties on the new platform. "Clients don’t always understand the impact, and hackers can sometimes achieve more than you would expect. We offered to pay hackers not just for finding vulnerabilities, but also for combining vulnerabilities into chains and sequences."
Evgeny Voloshin, Head of Expert Services, BI.ZONE, believes that bug bounties have become mainstream in Russia. "We’ve got three platforms launching almost simultaneously. This speaks to a market demand and a real need. Large platforms have their own issues, their own histories, but we aren’t bogged down by any kind of legacy. We have an opportunity to make everything awesome right out of the gate," he said.
Russian Ministry of Digital Development, Communications, and Mass Media Cybersecurity Director Vladimir Bengin is confident that, with some help from experts, the issues associated with the development of bug bounty platforms in Russia can be overcome. "At the Ministry, we’ve been hearing people talking about how bug bounties can be treated as a kind of gray area. We expect experts and people who have experience in this field to tell us how they would solve this problem. If we need to pass a law or take some other steps, we’re open to that."
The topic of bug bounties and the appearance of the new platform, The Standoff 365 Bug Bounty, was also discussed by Vladimir Zapolyansky and his guests in the PHDays 11 on-air studio.
"We bring business and hackers together," said Yaroslav Babin, The Standoff 365 Product Director. "Our goal is to get people from both camps involved. We’ve always had a good relationship with the hacking community. We’ve got the PHDays forum and The Standoff cyberexercises. We haven’t even launched yet, and 366 hackers have already registered on the platform. We won’t have any problems with research, and our community will continue to grow."
Dmitry Kuzevanov, Technical Director of Azbuka Vkusa, believes that, prior to the launch of the Positive Technologies platform, there was simply no decent platform on the Russian market because it needed to be trusted by both companies and hackers. "There’s a new platform now, and we’re eager to join it. We’re impressed by its reputation, confidence, and hacker traffic. We can trust Positive Technologies in this matter," he said.
This ends our coverage of Positive Hack Days 11 and The Standoff. Follow our social media pages to keep up with all the latest news.
We remind you that Positive Technologies is the permanent organizer of PHDays and The Standoff. For the third time running, the Innostage group of companies was the co-organizer. Innostage experts deploy and maintain the cyberrange infrastructure. Specialists from the CyberART cyberthreat prevention center monitor the battle, supervise team actions, act as mentors for one of the defense teams, and demonstrate implemented attack chains to the forum guests.
The business partners of the forum are Security Vision, a developer of cybersecurity solutions, Rostelecom-Solar, a national provider of information security services and technologies, and MONT, a distributor of software for any business. The technological partner is Azbuka Vkusa. The partners of PHDays 11 are Axoft, Fortis, Gazinformservice, IBS Platformix, ICL System Technologies, InfoWatch, Jet Infosystems, Liberum Veritas, Marvel Distribution, Pangeo Radar, R-Vision, and USSC.